
Stanford University says the personal information of 27,000 individuals was stolen in a ransomware attack impacting its Department of Public Safety (SUDPS) network.
The university discovered the attack on September 27 and disclosed one month later that it was investigating a cybersecurity incident impacting SUDPS systems.
In an update published on Monday, Stanford said the attackers didn’t gain access to other systems outside the Department of Public Safety’s network.
“The investigation determined that an unauthorized individual(s) gained access to the Department of Public Safety’s network between May 12, 2023, and Sept. 27, 2023,” the university said.
According to data breach notifications filed with Maine’s Attorney General, the attackers stole documents containing personally identifiable information (PII) belonging to 27,000 individuals.
“The personal information that may have been affected varies from person to person but could include date of birth, Social Security number, government ID, passport number, driver’s license number, and other information the Department of Public Safety may have collected in its operations,” Stanford added.
“For a small number of individuals, this information may also have included biometric data, health/medical information, email address with password, username with password, security questions and answers, digital signature, and credit card information with security codes.”
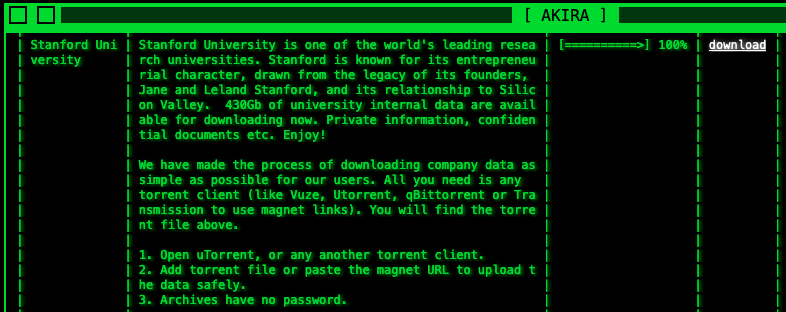
While Stanford has not attributed the September incident to a specific ransomware operation, the Akira ransomware gang claimed the attack in October, saying they stole 430Gb of files from the university’s systems.
The cybercrime group has since published the stolen data on their dark web leak site, making it available for download via BitTorrent.
The Akira ransomware operation emerged in March 2023 and quickly gained notoriety by targeting victims across various industry verticals.
By June 2023, the Akira ransomware operators had developed and deployed a Linux encryptor to target VMware ESXi virtual machines widely used in enterprise environments.
According to negotiation chats seen by BleepingComputer, the ransomware group is asking for ransom payments ranging from $200,000 to millions of dollars, depending on the size of the breached organization.
Stanford University disclosed another data breach in February 2023 after Department of Economics Ph.D. program admission information was exposed online between December 2022 and January 2023.
The incident followed an April 2021 data breach after the Clop ransomware leaked documents stolen from Stanford School of Medicine’s Accellion File Transfer Appliance (FTA) platform.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.