
A new campaign targeting vulnerable Docker services deploys an XMRig miner and the 9hits viewer app on compromised hosts, allowing a dual monetization strategy.
9hits is a web traffic exchange platform where members can drive traffic to each others’ sites.
This traffic is generated by a 9hits viewer app that is installed on members’ devices, which uses a headless Chrome instance to visit websites requested by other members. In return, those users earn credits, which can be used to pay for traffic to their own sites.
In a campaign discovered by Cado Security, attackers deploy the 9hits viewer app on compromised Docker hosts to generate credits for themselves, exploiting the resources of those systems to drive traffic as part of the 9hits traffic exchange system.
“This is the first documented case of malware deploying the 9hits application as a payload,” explains a report by Cado Security shared with BleepingComputer.
Attack details
While it’s not clear how the threat actors find systems to breach, Cado believes the attackers likely use a network scanning product like Shodan to discover vulnerable servers and breach them to deploy malicious containers via the Docker API.
The containers are in images sourced from Dockerhub to reduce suspicion. The spreader script captured in Cado’s Docker honeypot uses Docker’s CLI to set the DOCKER_HOST variable and uses typical API calls to pull and run the containers.
The 9hits container runs a script (nh.sh) with a session token, allowing it to authenticate and generate credits for the attacker by visiting a list of websites.
The session token system is designed to operate securely, even in untrusted environments, allowing the attacker to generate profit without risking getting banned.
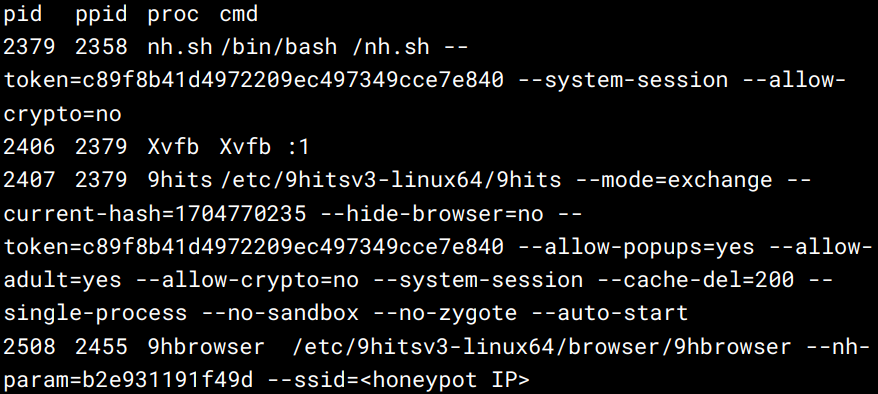
The attackers have set specific arguments for the 9hits app, such as allowing popups or visiting adult sites but disallowing cryptocurrency-related sites.
The other container runs an XMRig miner that mines Monero cryptocurrency for the attacker, using the cloud system’s resources.
The miner connects to a private mining pool, making tracing the campaign’s scale or profits impossible. Cado notes that the domain used for the mining pool suggests the attacker might use dynamic DNS services to maintain control.
“The main impact of this campaign on compromised hosts is resource exhaustion, as the XMRig miner will use all available CPU resources it can while 9hits will use a large amount of bandwidth, memory, and what little CPU is left,” comments Cado Security in the report.
“The result of this is that legitimate workloads on infected servers will be unable to perform as expected.”
The campaign discovered by Cado shows that threat actors are constantly exploring alternative monetization channels beyond traditional methods like cryptomining, diversifying their attacks, and following more covert avenues.
Platforms abused by threat actors, such as 9hits, need stricter security checks and policies to prevent unauthorized use of their apps that can cause financial damage and disruption to organizations.
Entities investing in cloud computing environments are called to navigate a complicated landscape.
Achieving this requires using zero-trust models, Cloud Workload Protection Platforms (CWPP), and Cloud Security Posture Management (CSPM) to improve visibility, manage configurations, and protect exposed assets.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.