Multiple proof-of-concept (PoC) exploits for a critical Jenkins vulnerability allowing unauthenticated attackers to read arbitrary files have been made publicly available, with some researchers reporting attackers actively exploiting the flaws in attacks.
Jenkins is an open-source automation server widely used in software development, particularly for Continuous Integration (CI) and Continuous Deployment (CD).
It plays a critical role in automating various parts of the software development process, like building, testing, and deploying applications. It supports over a thousand integration plugins and is used by organizations of all sizes, including large enterprises.
SonarSource researchers discovered two flaws in Jenkins that could enable attacks to access data in vulnerable servers and execute arbitrary CLI commands under certain conditions.
The first flaw, rated critical, is CVE-2024-23897, allowing unauthenticated attackers with ‘overall/read’ permission to read data from arbitrary files on the Jenkins server.
Attackers without this permission can still read the first few lines of files, with the number depending on the available CLI commands.
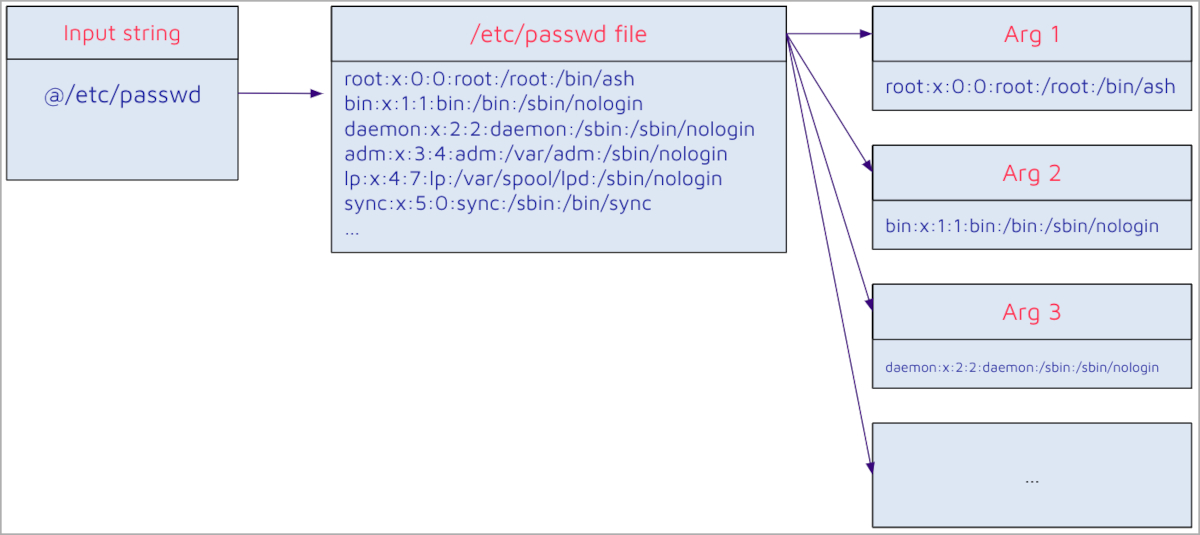
The flaw stems from the default behavior of the args4j command parser in Jenkins, which automatically expands file contents into command arguments when an argument starts with the “@” character, allowing unauthorized reading of arbitrary files on the Jenkins controller file system.
Sonar explained that exploitation of the particular flaw could lead to admin privilege escalation and arbitrary remote code execution. This step, however, depends on certain conditions that must be met, which are different for each attack variant.
The second flaw, tracked as CVE-2024-23898, is a cross-site WebSocket hijacking issue where attackers could execute arbitrary CLI commands by tricking a user into clicking a malicious link.
This risk that arises from this bug should be mitigated by existing protective policies in web browsers, but it persists due to the lack of universal enforcement of these policies.
SonarSource reported the flaws to the Jenkins security team on November 13, 2023, and helped verify the fixes in the following months.
On January 24, 2024, Jenkins released fixes for the two flaws with versions 2.442 and LTS 2.426.3, and published an advisory that shares various attack scenarios and exploitation pathways, as well as fix descriptions and possible workarounds for those unable to apply the security updates.
Exploits available
With abundant information about the Jenkins flaws now available, many researchers reproduced some of the attack scenarios and created working PoC exploits published on GitHub.
The PoCs are for CVE-2024-23897, which gives attackers remote code execution on unpatched Jenkins servers.
Many of these PoCs have already been validated, so attackers scanning for exposed servers can grab the scripts and try them out with minimal or no modification.
Some researchers report that their Jenkins honeypots have already caught activity in the wild, suggesting that hackers have started exploiting the vulnerabilities.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.