
GitHub is warning users that they will soon have limited functionality on the site if they do not enable two-factor authentication (2FA) on their accounts.
In emails sent to GitHub users on Christmas Eve, the company warned that all users contributing code on GitHub.com must enable 2FA by January 19th, 2024.
“This is a reminder that we announced that we are requiring users contributing code on GitHub.com to enable two-factor authentication (2FA),” reads the email seen by BleepingComputer.
“You are receiving this notification because your account meets this criteria and will be required to enroll in 2FA by January 19th, 2024 at 00:00 (UTC)”.
This same warning is shown on the GitHub site after logging into your account, as shown below.
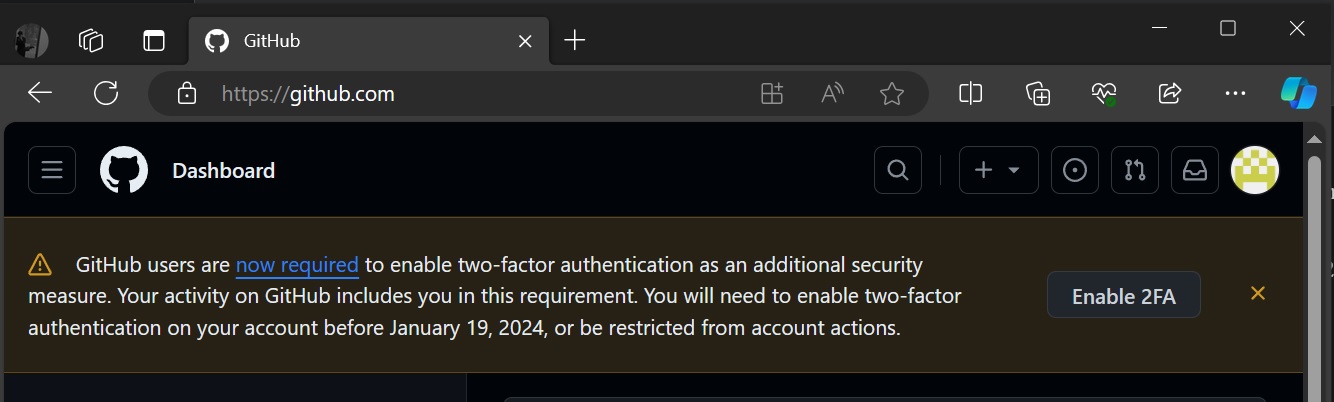
Source: BleepingComputer
If you write or manage code on GitHub, this will apply to you. The company has made this decision to protect accounts from being breached and code altered in supply chain attacks.
However, this change is only for GitHub.com, not for business or enterprise accounts.
If you haven’t set up 2FA by the deadline, you’ll find your access to GitHub limited. But don’t worry, GitHub has instructions to help you configure it easily.
“On January 19th, 2024 at 00:00 (UTC) your account will be required to have 2FA for authentication. If you have not yet enrolled by that date, your ability to access GitHub.com will be limited until you finish the enrollment process,” the company noted in an email to its users.
After the January 19th deadline, users attempting to access GitHub.com without 2FA will be automatically directed to complete the setup.
Even after 2FA becomes mandatory, any configured Personal Access Tokens, SSH keys, and apps will still work. However, if you want to make new ones or change your account settings, you must enable 2FA on the account.
How to setup 2FA on Github
GitHub offers various methods for enabling 2FA, catering to user preferences regarding using security keys, GitHub Mobile, authenticator apps (TOTP), and SMS text messages.
To guarantee continuous access, activating at least two of these methods is recommended. Users can manage their 2FA settings and explore additional methods in their security settings on GitHub.
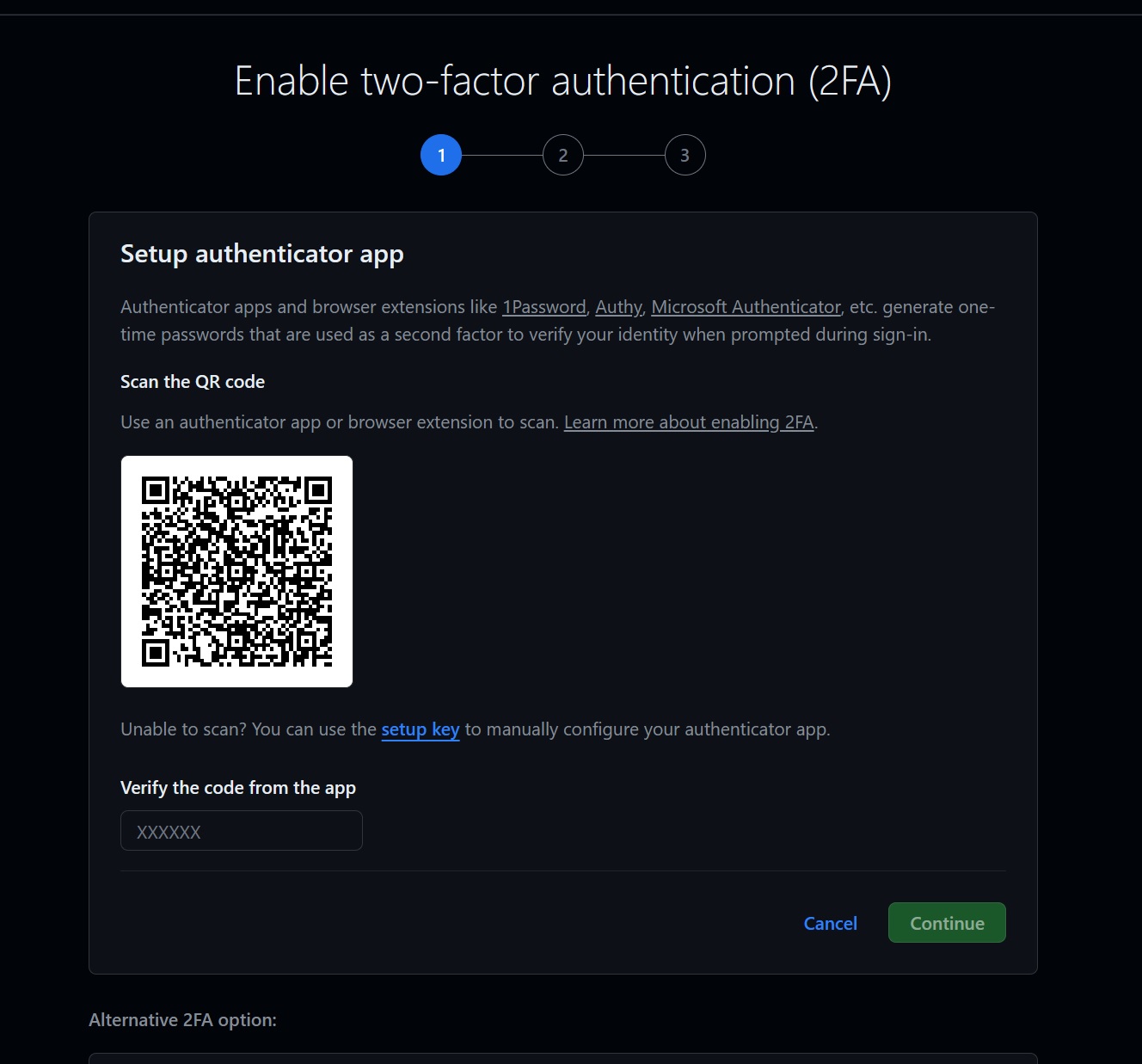
Source: BleepingComputer
If you’ve already enabled 2FA before January 19th, 2024, you’re all set. After that date, you can’t turn off 2FA, but you can change your configured verification methods.
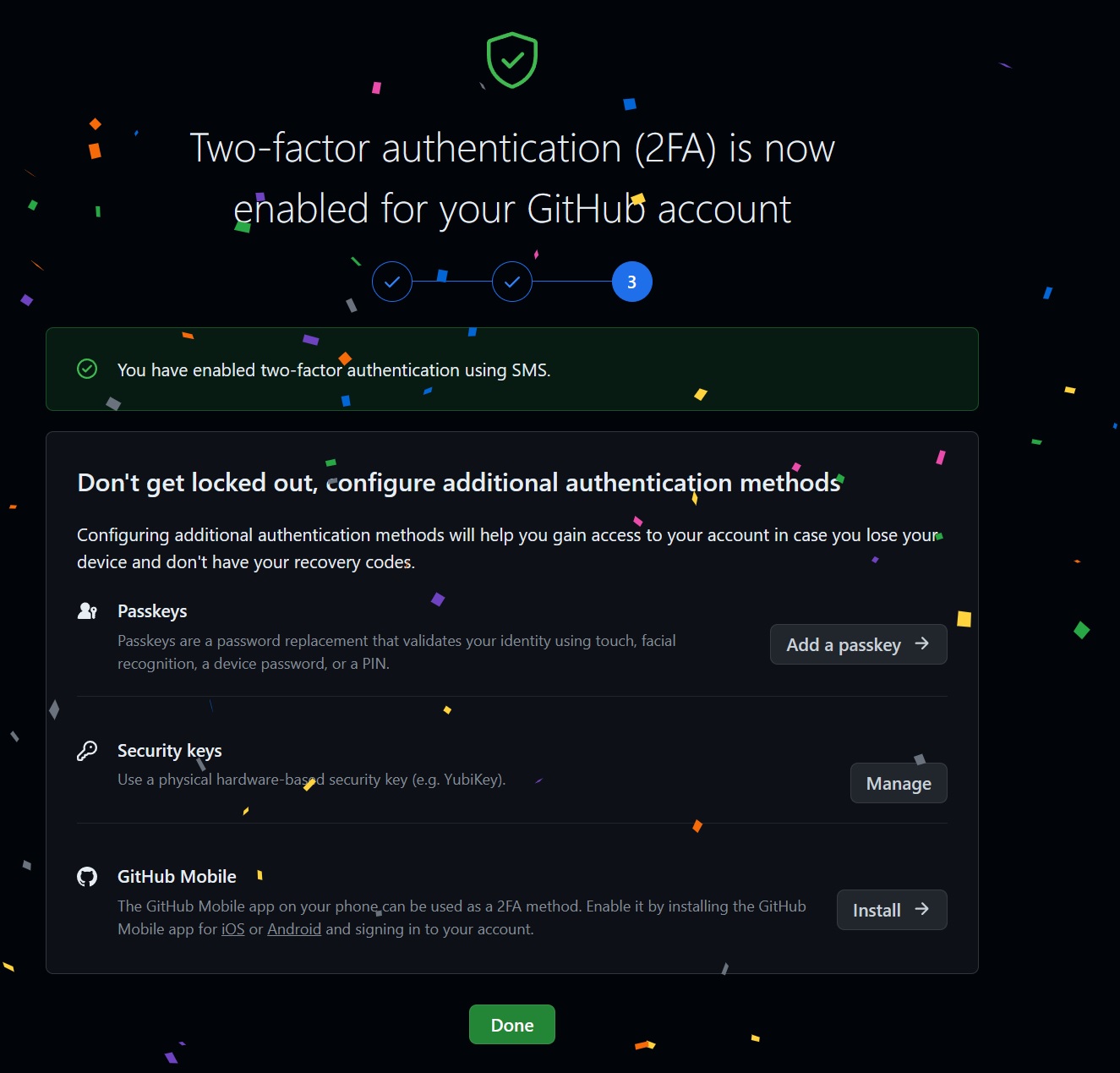
Source: BleepingComputer
In its email, GitHub suggests having more than one 2FA method, as it warned that it “may not be able to restore access to accounts with 2FA enabled if you lose your 2FA credentials”.
If you lose all your 2FA options, the only way back into your account is with your recovery codes.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.