
The source code for Grand Theft Auto 5 was reportedly leaked on Christmas Eve, a little over a year after the Lapsus$ threat actors hacked Rockstar games and stole corporate data.
Links to download the source code were shared on numerous channels, including Discord, a dark web website, and a Telegram channel that the hackers previously used to leak stolen Rockstar data.
In a post to a Grand Theft Auto leak channel on Telegram, the channel owner known as ‘Phil’ posted links to the stolen source code, sharing a screenshot of one of the folders.
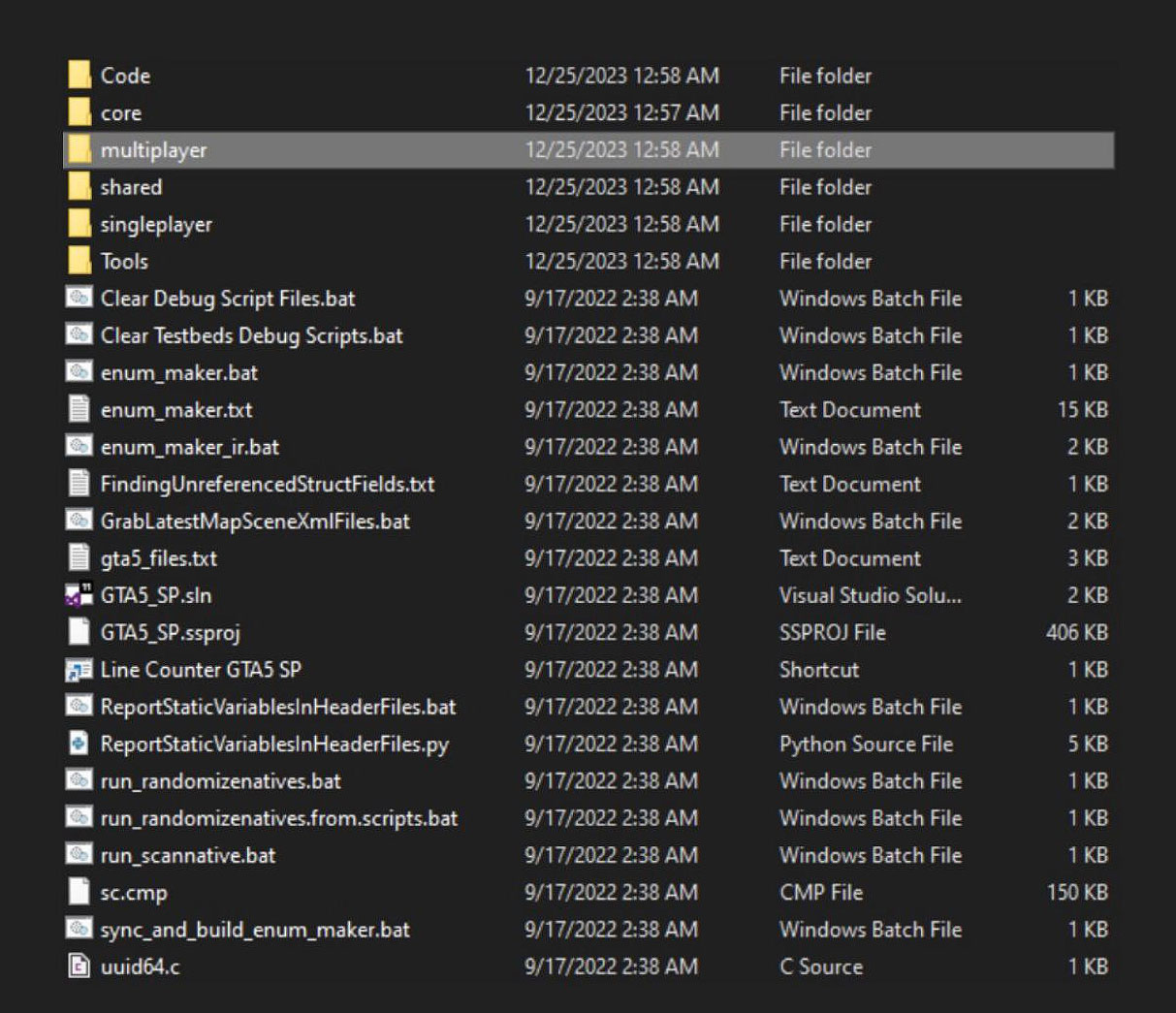
Source: Telegram
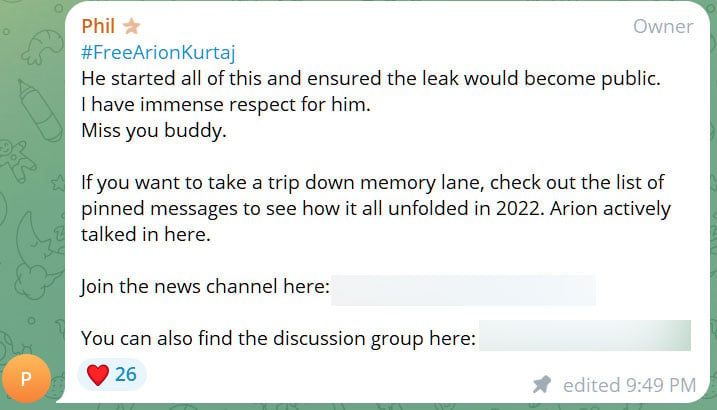
The channel owner also paid homage to Lapsus$ hacker Arion Kurtaj, who previously leaked pre-release videos of Grand Theft Auto 6 under the name ‘teapotuberhacker.’
Kurtaj was recently sentenced to an indefinite hospital stay by a UK judge for hacking into Rockstar and Uber.
“#FreeArionKurtaj
He started all of this and ensured the leak would become public.
I have immense respect for him.
Miss you buddy.
If you want to take a trip down memory lane, check out the list of pinned messages to see how it all unfolded in 2022. Arion actively talked in here.”
Rockstar Games was hacked in 2022 by members of the notorious Lapsus$ hacking group, who gained access to the company’s internal Slack server and Confluence wiki.
At the time, the threat actors claimed to have stolen the GTA 5 and GTA 6 source code and assets, including a GTA 6 testing build, with some of the stolen content leaked on forums and Telegram. The threat actor also shared GTA 5 source code samples as proof that they had stolen the data.
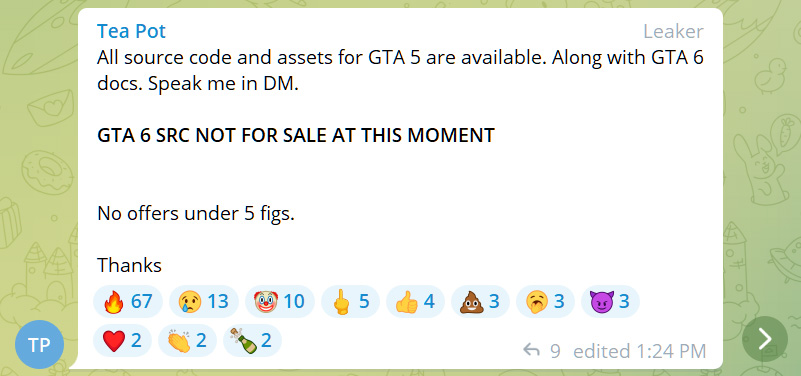
Source: BleepingComputer
Security research group vx-underground says they spoke to the leaker on Discord, who said the source code was leaked sooner than expected.
“They claim to have received the source code August, 2023,” reads a post by vx-underground.
“Their motivation was to combat scamming in the GTA V modding scene, many people were allegedly scammed by people claiming to have the GTA V source code.”
While BleepingComputer reviewed the leak, which appears to be legitimate GTA 5 source code, we could not independently verify its authenticity.
BleepingComputer contacted Rockstar about the leak but did not receive a response, likely due to the holidays.
The Lapsus$ hackers
The Lapsus$ hackers stood out for their skills at performing social engineering and SIM swapping attacks to breach corporate networks.
Some known cyberattacks attributed to the hacking group include Uber, Microsoft, Rockstar Games, Okta, Nvidia, Mercado Libre, T-Mobile, Ubisoft, Vodafone, and Samsung.
As part of these attacks, the threat actors would attempt to extort the companies not to leak stolen data, which in many cases was source code and customer data.
The success of these attacks led the Department of Homeland Security (DHS) Cyber Safety Review Board to analyze their tactics and share recommendations for preventing similar attacks in the future.
While the Lapsus$ group has not been very active after members were arrested, BleepingComputer was told some of the members are now believed to be active in the loose-knit hacking collective known as Scattered Spider.
Scattered Spider shares similar tactics to Lapsus$, utilizing social engineering, phishing, MFA fatigue, and SIM swapping attacks to gain initial network access to large organizations.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.