Malicious actors were detected abusing the open-source hypervisor platform QEMU as a tunneling tool in a cyberattack against a large company.
QEMU is a free emulator and hypervisor that allows you to run other operating systems as guests on a computer.
As part of the attack, threat actors used QEMU to create virtual network interfaces and a socket-type network device to connect to a remote server. This allowed the threat actors to create a network tunnel from the victim’s system to the attacker’s server with negligible impact on system performance.
This unusual case, which highlights the diverse methods attackers use to remain stealthy, was discovered by Kaspersky analysts who were called to investigate suspicious activity in the breached company’s systems.
Stealthy network tunnels
Hackers create network tunnels to establish a stealthy and secure communication channel between them and a compromised system.
Typically, these tunnels encrypt network traffic to help bypass firewalls, intrusion detection systems, and other security measures.
Kaspersky says that in 10% of the cases it has investigated in the past three years, hackers have used the FRP and ngrok utilities to create tunnels. Other tunneling tools used in attacks include CloudFlare tunnels, Stowaway, ligolo, 3proxy, dog-tunnel, chisel, gs-netcat, plink, iox, and nps.
Due to their frequent abuse by cybercriminals, defenders and monitoring tools treat these tools with suspicion.
In this unusual case involving QEMU, the attackers decided to leverage a less conventional tool for creating network tunnels that would unlikely raise any alarms, even if that meant giving up traffic encryption.
Additionally, QEMU offers unique capabilities such as emulating a wide range of hardware and virtual networks, allowing malicious activities to blend in with benign virtualization traffic, and bridging segmented network parts through strategically set up VM pivot points.
Feather-light backdoor
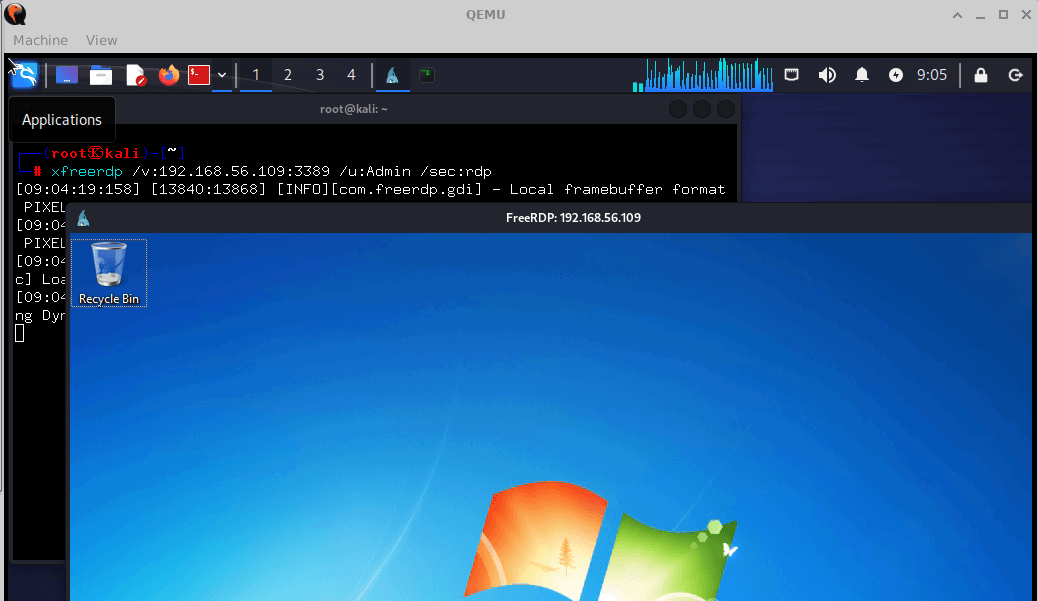
In the attack seen by Kaspersky, the hackers utilized ‘Angry IP Scanner’ for network scanning, ‘mimikatz’ for credential theft, and QEMU for creating a sophisticated network tunneling setup that facilitated a covert communication channel.
The attackers attempted to keep their footprint as minimal as possible, only allocating 1MB of RAM to the virtual machine they created, greatly reducing the chances of detection through resource consumption.
The configuration of the VM, which was started without using a LiveCD or disk image, includes the following arguments:
- -netdev user,id=lan,restrict=off: Configures a network backend named ‘lan’ in user mode, allowing unrestricted network access through the host’s network stack.
- -netdev socket,id=sock,connect=<IP>:443: Establishes a socket connection to a specified IP address on port 443, creating a direct network link for the backend ‘sock’.
- -netdev hubport,id=port-lan,hubid=0,netdev=lan/sock: Links a network device (either lan or sock) to a virtual hub hubid=0, facilitating network connectivity between different backends.
- -nographic: Runs QEMU without a graphical interface, opting for command-line interaction only, reducing its visibility and resource footprint.
Kaspersky conducted simulated tests to replicate the attackers’ specific use of QEMU, concluding that the setup looked like the one in the diagram below.
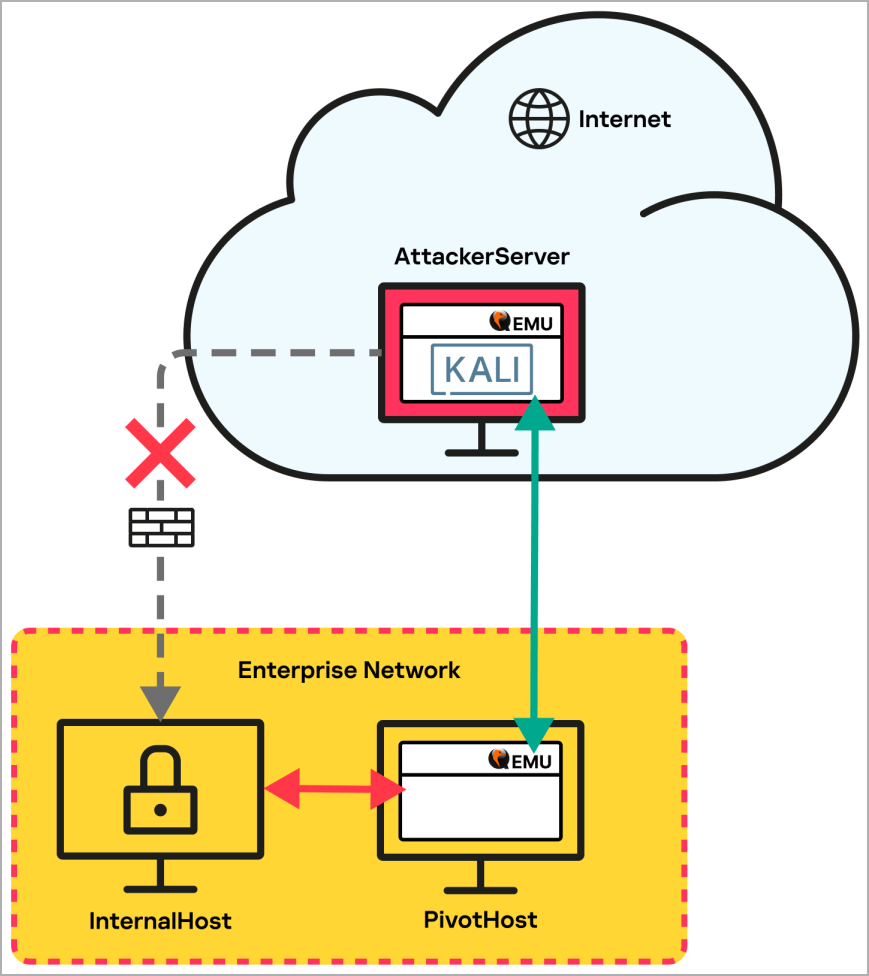
Using QEMU, the attackers established a network tunnel from the targeted internal host that didn’t have internet access to a pivot host with internet access, which in turn connects to the attacker’s server on the cloud, running a Kali Linux VM.
The ability of QEMU VMs to link seamlessly and bridge segmented network components is key in bypassing security measures and may also be used to further the breach laterally.
Kaspersky says that the enterprise should adopt multi-level protection to detect the use of legitimate tools like this, including 24/7 network monitoring, which may be outside the price point for many small businesses.
“This further supports the concept of multi-level protection, which covers both reliable endpoint protection, and specialized solutions for detecting and protecting against complex and targeted attacks including human-operated ones,” concluded Kaspersky.
“Only comprehensive security that includes 24/7 network (NDR, NGFW) and endpoint (EDR, EPP) monitoring, by SOC experts for one, can detect anomalies in a timely manner and block an attack in its initial stage.”
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.