Users of the social media platform X (formerly Twitter) have often been left puzzled when they click on a post with an external link but arrive at an entirely unexpected website from the one displayed in the post.
A Twitter ad spotted below by a security researcher shows forbes.com as its destination but instead takes you to a Telegram account purportedly promoting crypto scams.
Don’t trust link previews on X
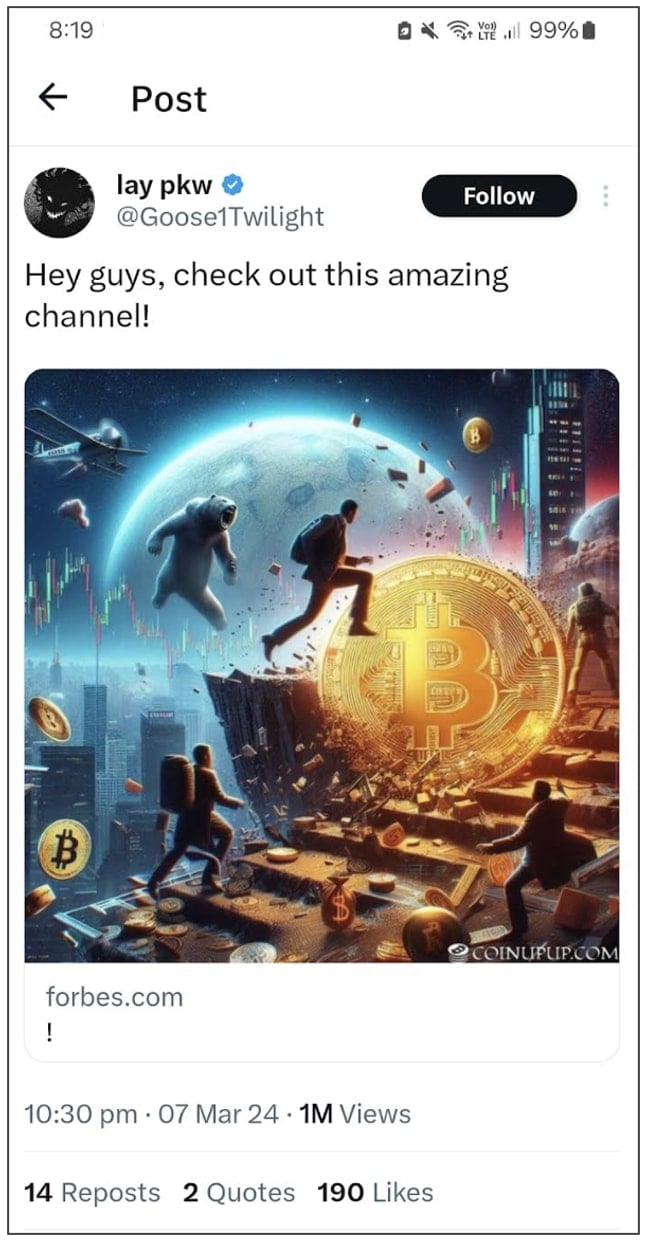
Security researcher Will Dormann spotted a Twitter post with a link to “forbes.com.”
The post from a verified account, when seen by the researcher, was being promoted as an ad on the platform too:
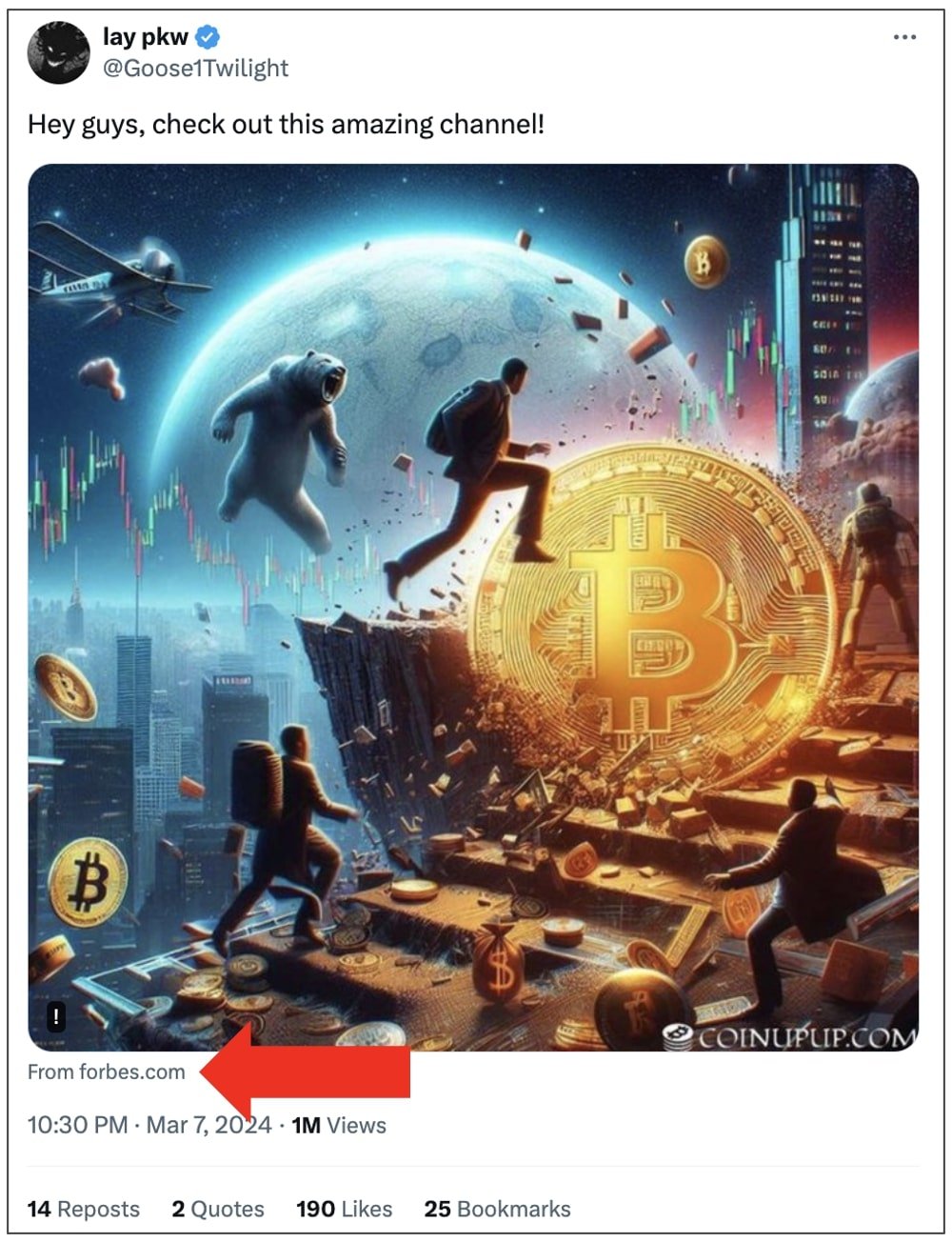
(BleepingComputer)
Clicking on the link in a web browser, however, would instead redirect a majority of the users to a “Crypto with Harry” Telegram account, which appears to offer dubious cryptocurrency advice:
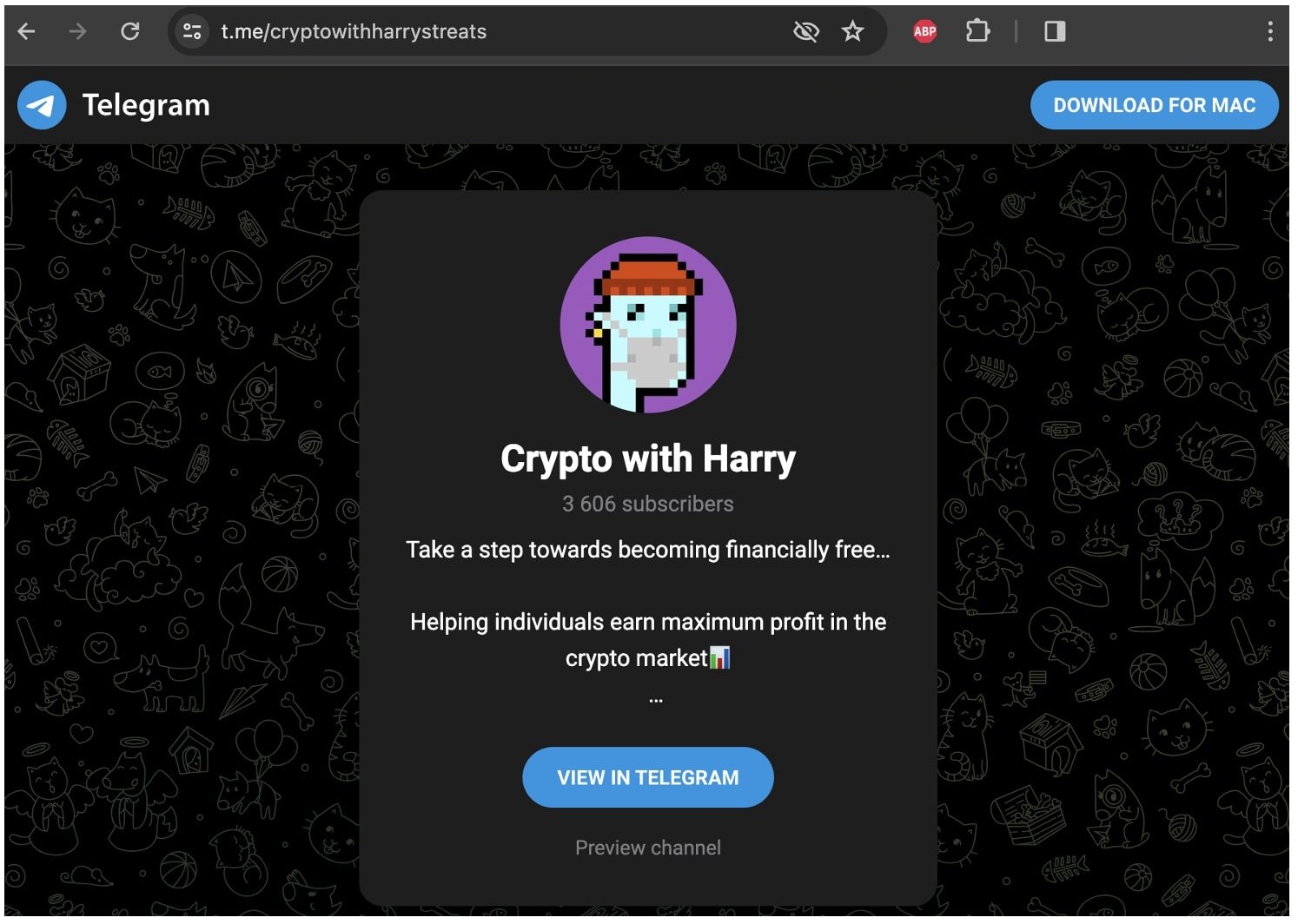
(BleepingComputer)
Why does this happen?
While external link previews should ideally show the first immediate domain a link takes you to when you click on it, X does the opposite.
The social media platform tries to determine (albeit unsuccessfully) the ultimate destination where a URL takes you and shows that as the website name, in a post.
The post in question, is actually, first taking users to a website called joinchannelnow[.]net which has been operational since January 29th this year (and surprise, registered on Namecheap).
Unlike X, Google Chrome shows you this (first) destination when you hover over the link:
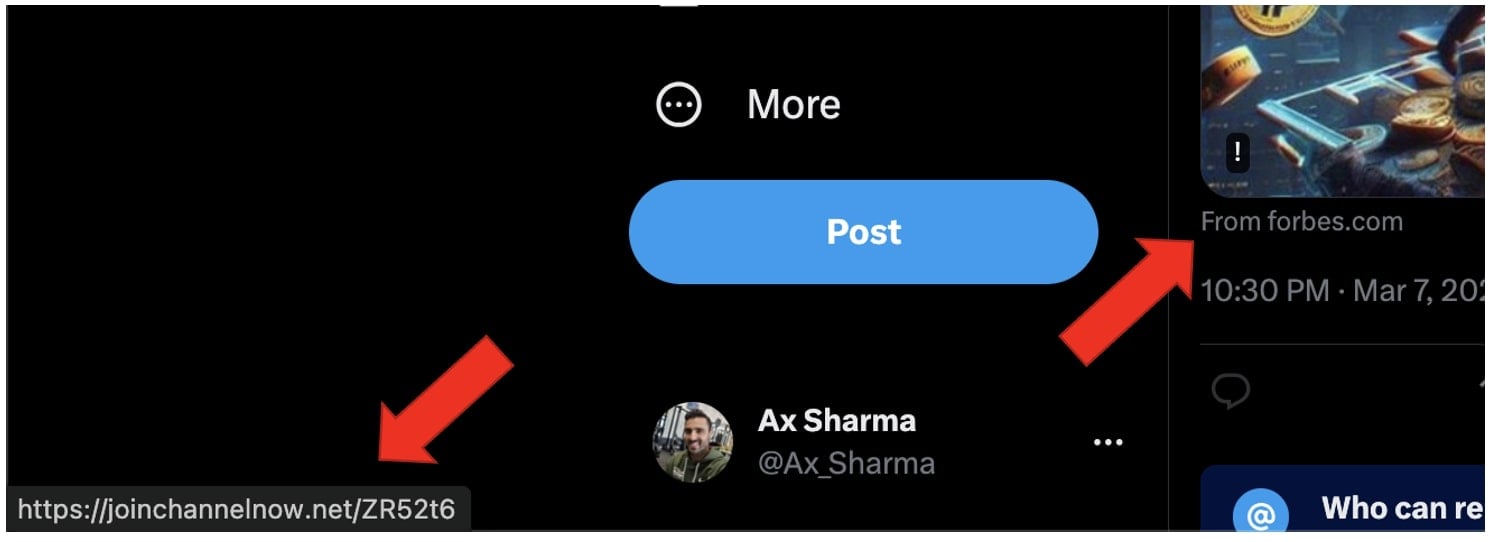
(BleepingComputer)
Once a user arrives at joinchannelnow[.]net, its server determines whether a request originates from a web browser or a bot—such as Twitter’s, being used to generate link previews.
It does so by checking the User-Agent HTTP header within an incoming request.
If a request is coming from a web browser, meaning most likely a human clicked on the link, joinchannelnow happily and sneakily redirects the user to the Telegram account shown above.
Otherwise, when it suspects that a bot or an automated tool is in use to trace where joinchannelnow ultimately redirects to, it redirects the request to a legitimate forbes.com article:
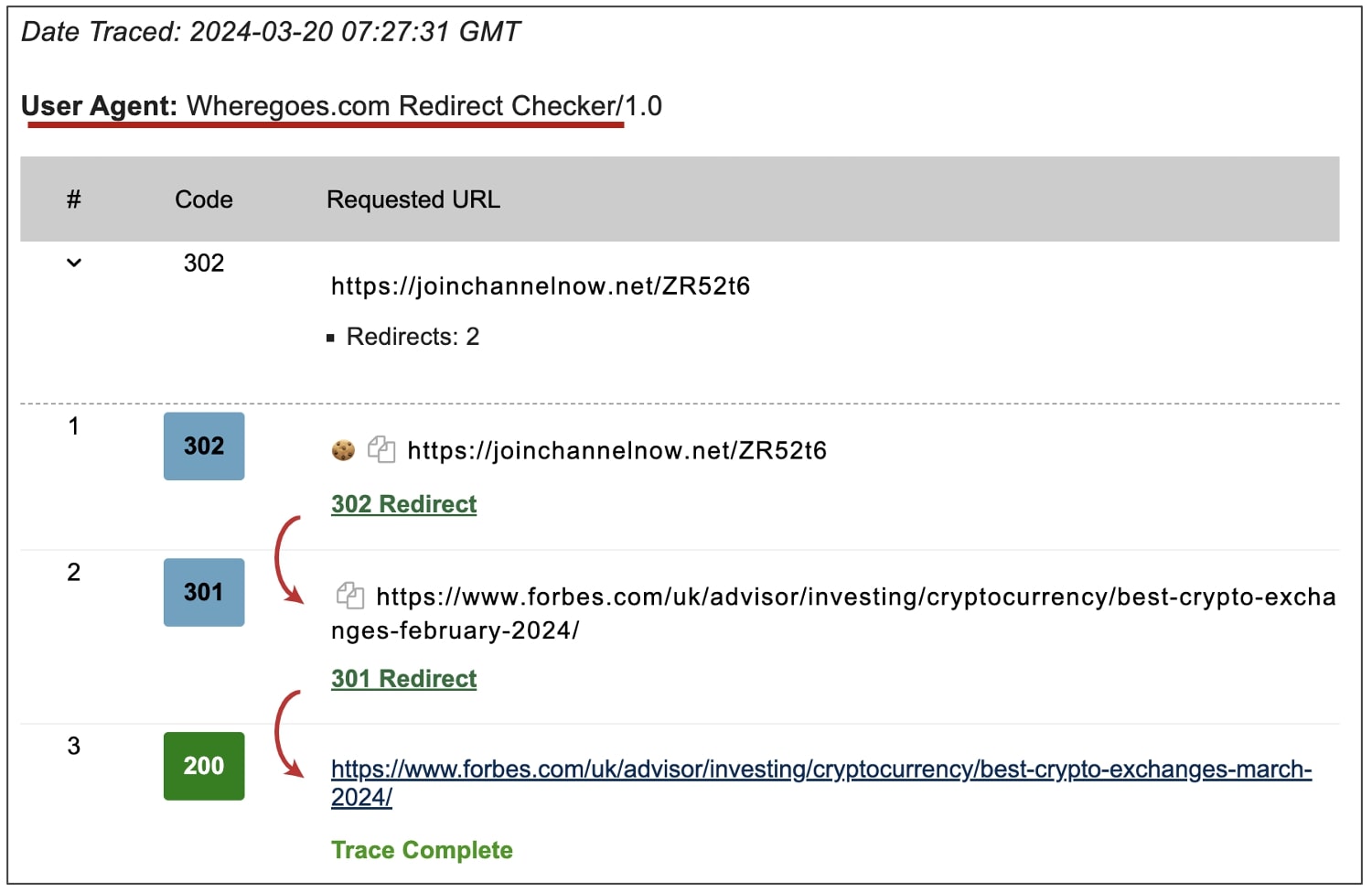
(BleepingComputer via Wheregoes.com)
This is how X can be fooled into showing a website name in a post (or worse, an ad) which is completely different from where users would be arriving.
The flaw is especially problematic on X mobile apps as, unlike in a Desktop web browser where one could easily hover over the link to see where it’s taking them, that functionality (i.e. a status bar) is completely absent on mobile.
That means users will only see “forbes.com” on the app and, after tapping the preview, immediately arrive at the Telegram account in question.
The slick trick can be abused by all kinds of adversaries, from crypto scammers to those pushing malware, trojanized app installs, phishing, and spam services to prey on unsuspecting users.
Reddit posts seen by BleepingComputer imply that this flaw has been known to and exploited by threat actors for quite some time.
Suffice to say, it’s best not to click on external links in Twitter posts and ads without hovering over them and paying close attention to the URL shown in your browser’s status bar. On mobile devices, it’s safest to not tap on posts with links at all.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.