
The notorious North Korean hacking group known as Lazarus continues to exploit CVE-2021-44228, aka “Log4Shell,” this time to deploy three previously unseen malware families written in DLang.
The new malware are two remote access trojans (RATs) named NineRAT and DLRAT and a malware downloader named BottomLoader.
The D programming language is rarely seen in cybercrime operations, so Lazarus probably chose it for new malware development to evade detection.
The campaign, which Cisco Talos researchers codenamed “Operation Blacksmith,” started around March 2023 and targets manufacturing, agricultural, and physical security companies worldwide.
Operation Blacksmith represents a notable shift in tactics and tools used by Lazarus, serving as yet another demonstration of the threat group’s ever-shifting tactics.
New malware tools
The first malware, NineRAT, is Lazarus’ first of the two novel RATs. It uses the Telegram API for command and control (C2) communication, including receiving commands and exfiltrating files from the breached computer.
NineRAT incorporates a dropper, which is also responsible for establishing persistence and launching the main binaries.
The malware supports the following commands, which are accepted via Telegram:
- info – Gather preliminary information about the infected system.
- setmtoken – Set a token value.
- setbtoken – Set a new Bot token.
- setinterval – Set time interval between malware polls to the Telegram channel.
- setsleep – Set a time period for which the malware should sleep/lie dormant.
- upgrade – Upgrade to a new version of the implant.
- exit – Exit execution of the malware.
- uninstall – Uninstall self from the endpoint.
- sendfile – Send a file to the C2 server from the infected endpoint.
The second malware, DLRAT, is a trojan and downloader that Lazarus can use to introduce additional payloads on an infected system.
DLRAT’s first activity on a device is to execute hard-coded commands to collect preliminary system information like OS details, network MAC address, etc., and send it to the C2 server.
The attacker’s server replies with the victim’s external IP address and one of the following commands for local execution by the malware:
- deleteme – Delete the malware from the system using a BAT file
- download – Download files from a specified remote location
- rename – Rename files on the infected system
- iamsleep – Instruct the malware to enter a dormant state for a set period
- upload – Upload files to the C2 server
- showurls – No implemented yet
Finally, Cisco’s analysts discovered BottomLoader, a malware downloader that fetches and executes payloads from a hardcoded URL using PowerShell while also establishing persistence from them by modifying the Startup directory.
In addition, BottomLoader offers Lazarus the capacity to exfiltrate files from the infected system to the C2 server, providing some operational versatility.
Log4Shell attacks
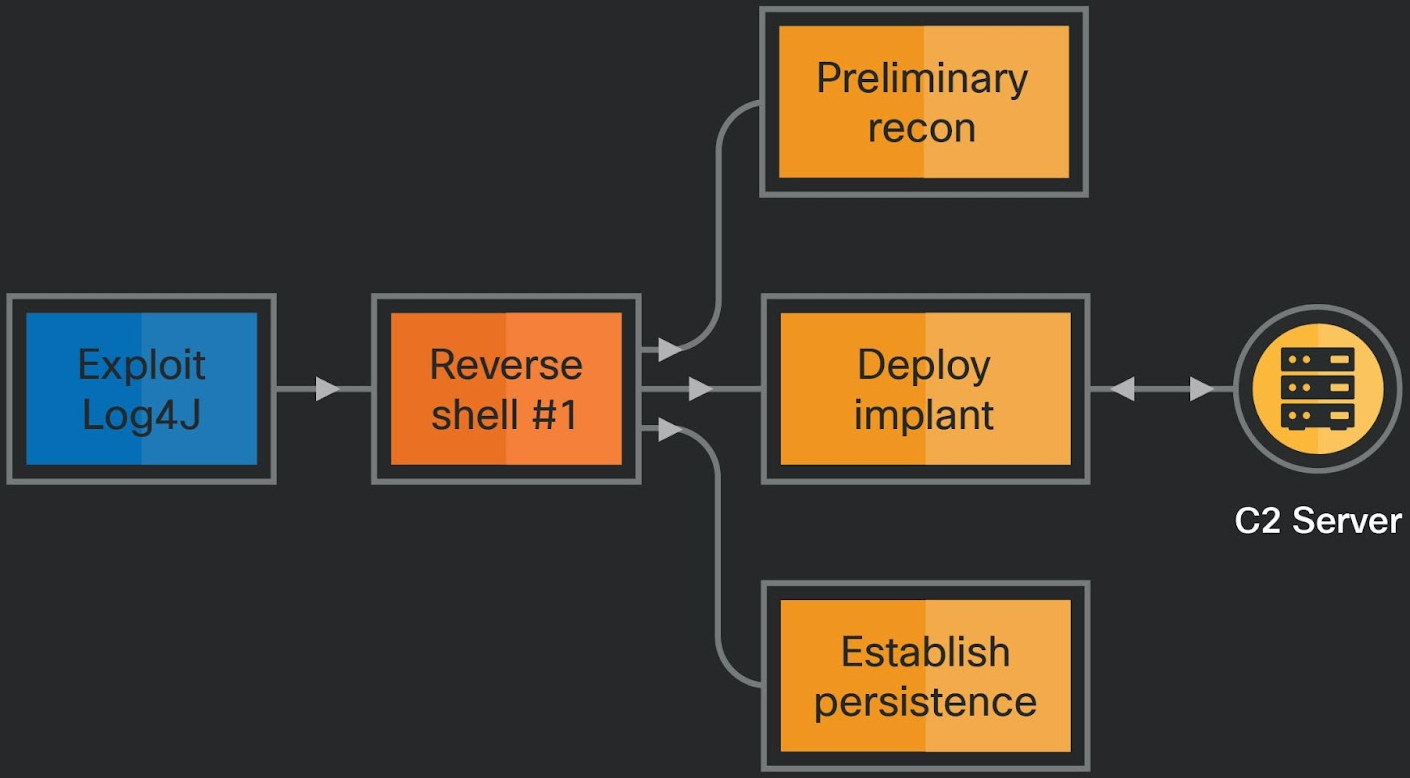
The attacks observed by Cisco Talos involve leveraging Log4Shell, a critical remote code execution flaw in Log4j, which was discovered and fixed approximately two years ago yet remains a security problem.
The targets are publicly facing VMWare Horizon servers, which use a vulnerable version of the Log4j logging library, allowing the attackers to perform remote code execution.
Following the compromise, Lazarus sets up a proxy tool for persistent access on the breached server, runs reconnaissance commands, creates new admin accounts, and deploys credential-stealing tools like ProcDump and MimiKatz.
In the second phase of the attack, Lazarus deploys the NineRAT on the system, which supports a wide range of commands, as highlighted in the previous section.
Cisco concludes that it’s possible Lazarus feeds other APT (advanced persistent threat) groups or clusters under its umbrella with data collected by NineRAT.
This assumption is based on the fact that NineRAT performs system “re-fingerprinting” in some cases, implying that it could be performing system IDing and data collection for multiple actors.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.