
A new phishing campaign pretending to be a ‘copyright infringement’ email attempts to steal the backup codes of Instagram users, allowing hackers to bypass the two-factor authentication configured on the account.
Two-factor authentication is a security feature that requires users to enter an additional form of verification when logging into the account. This verification is usually in the form of one-time passcodes sent via SMS text message, codes from an authentication app, or through hardware security keys.
Using 2FA helps protect your accounts if your credentials are stolen or purchased from a cybercrime marketplace, as the threat actor would need access to your mobile device or email to log into your protected account.
When configuring two-factor authentication on Instagram, the site will also provide eight-digit backup codes that can be used to regain access to accounts if you cannot verify your account using 2FA. This could happen for multiple reasons, such as switching your mobile number, losing your phone, and losing access to your email account.
However, backup codes come with some risk, as if a threat actor can steal those codes, they can hijack Instagram accounts using unrecognized devices simply by knowing the target’s credentials, which can be stolen through phishing or found in unrelated data breaches.
Copyright infringement phishing messages claim the recipient has posted something that violates intellectual property protection laws, and hence, their account has been restricted.
Recipients of these messages are urged to click a button to appeal the decision, which redirects them to phishing pages where they enter their account credentials and other details.
The same theme has been used several times, including against Facebook users, and has facilitated infection chains for the LockBit ransomware and the BazaLoader malware, among others.
New Instagram phishing campaign
The latest variant of these attacks was spotted by Trustwave analysts, who report that the increasing adoption rate of 2FA protection pushes phishing actors to broaden their targeting scope.
The latest phishing emails impersonate Meta, Instagram’s parent company, warning that Instagram users received copyright infringement complaints. The email then prompts the user to fill out an appeal form to resolve the issue.
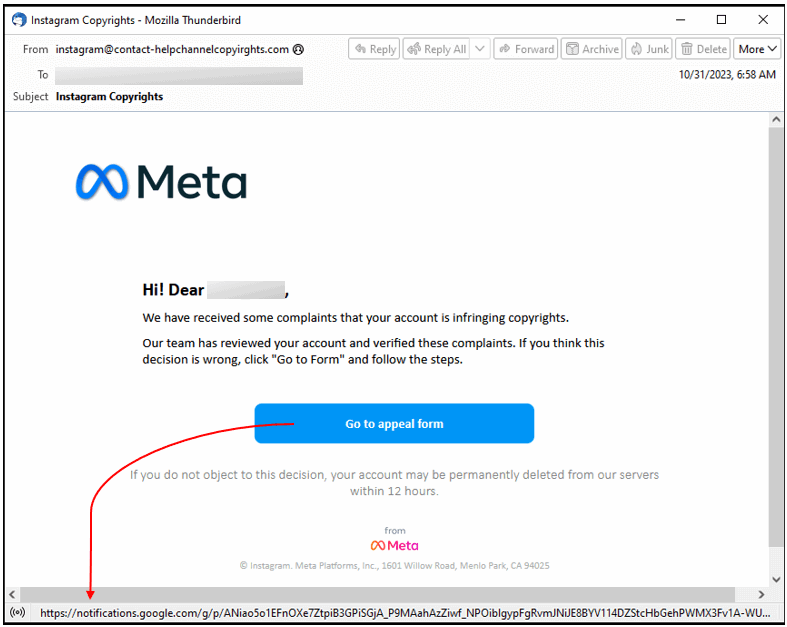
Clicking the button takes the target to a phishing site impersonating Meta’s actual violations portal, where the victim clicks a second button labeled “Go to Confirmation Form (Confirm My Account).”
The second button redirects to another phishing page designed to appear as Meta’s “Appeal Center” portal, where the victims are requested to enter their username and password (twice).
After siphoning these details, the phishing site asks the target if their account is protected by 2FA and, upon confirmation, requests the 8-digit backup code.
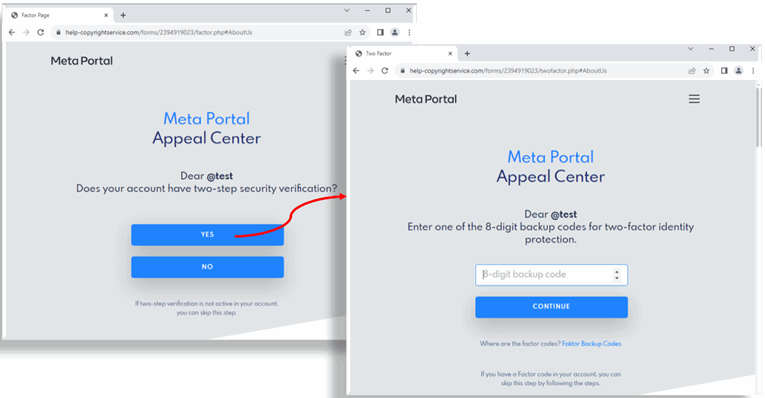
Despite the campaign being characterized by multiple signs of fraud, like the sender’s address, the redirection page, and phishing page URLs, the convincing design and sense of urgency could still trick a significant percentage of targets into giving away their account credentials and backup codes.
Backup codes are meant to be kept private and stored securely. Account holders should treat them with the same level of secrecy as their passwords and refrain from entering them anywhere unless necessary for accessing their accounts.
If you still have access to your 2FA codes/keys, there’s never a reason to enter your backup codes anywhere other than within the Instagram website or app.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.