
A previously unknown Android backdoor named ‘Xamalicious’ has infected approximately 338,300 devices via malicious apps on Google Play, Android’s official app store.
McAfee, a member of the App Defense Alliance, discovered 14 infected apps on Google Play, with three having 100,000 installs each.
Even though the apps have since been removed from Google Play, users who installed them since mid-2020 might still carry active Xamalicious infections on their phones, requiring manual scans and cleanup.
The most popular of the Xamalicious apps are the following:
- Essential Horoscope for Android – 100,000 installs
- 3D Skin Editor for PE Minecraft – 100,000 installs
- Logo Maker Pro – 100,000 installs
- Auto Click Repeater – 10,000 installs
- Count Easy Calorie Calculator – 10,000 installs
- Dots: One Line Connector – 10,000 installs
- Sound Volume Extender – 5,000 installs
Also, a separate set of 12 malicious apps carrying the Xamalicious threat, for which download stats aren’t available, are distributed on unofficial third-party app stores, infecting users via downloadable APK (Android package) files.
Source: McAfee
According to McAfee’s telemetry data, most infections were installed on devices in the United States, Germany, Spain, the U.K., Australia, Brazil, Mexico, and Argentina.
The Xamalicious Android backdoor
Xamalicious is a .NET-based Android backdoor embedded (in the form of ‘Core.dll’ and ‘GoogleService.dll’) within apps developed using the open-source Xamarin framework, making the analysis of its code more challenging.
Upon installation, it requests access to the Accessibility Service, enabling it to perform privileged actions like navigation gestures, hide on-screen elements, and grant additional permissions to itself.
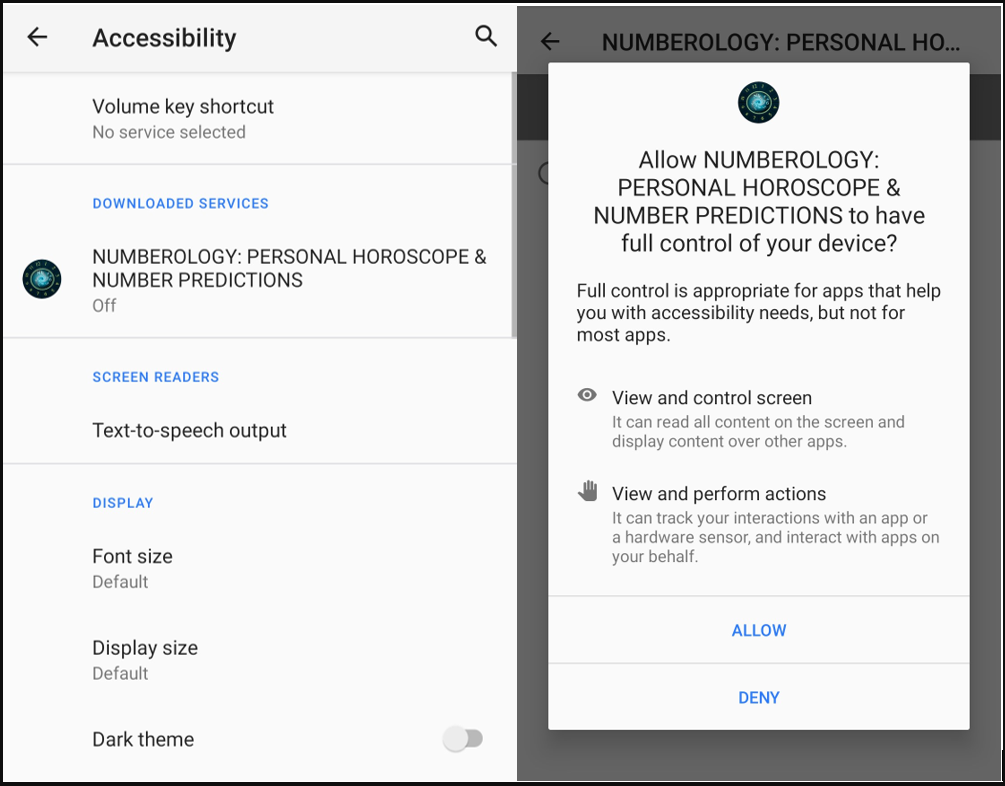
Source: McAfee
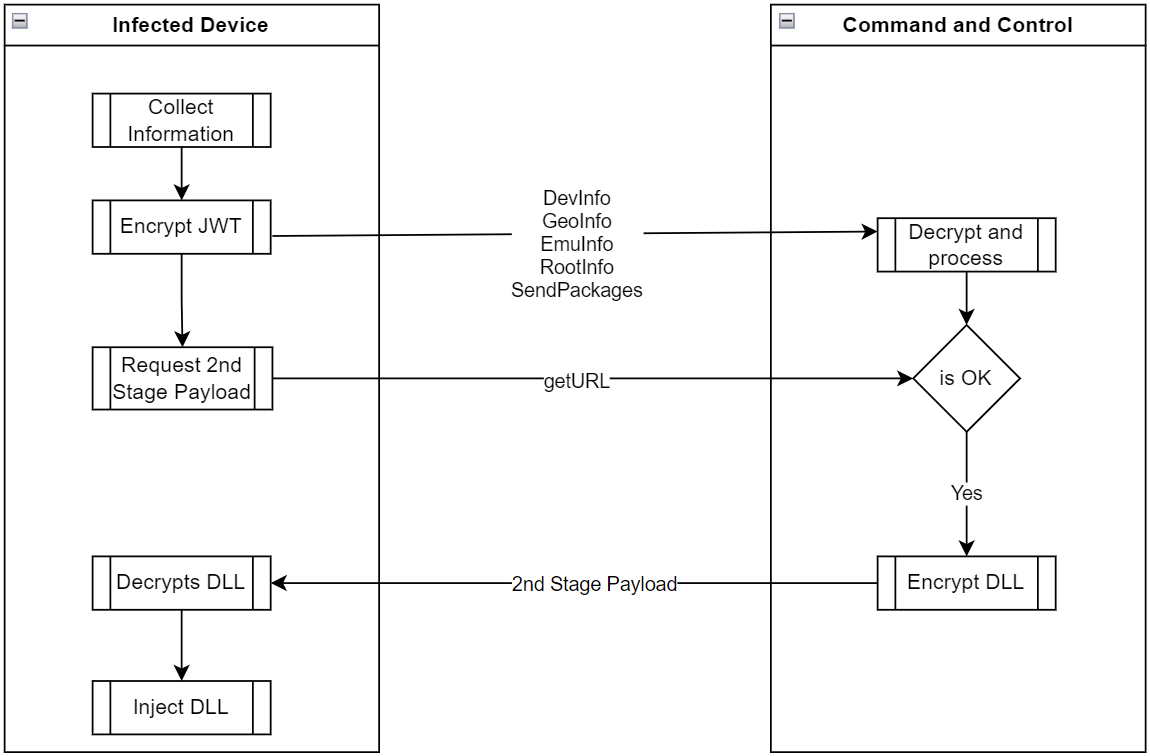
After installation, it communicates with the C2 (command and control) server to fetch the second-stage DLL payload (‘cache.bin’) if specific geographical, network, device configuration, and root status prerequisites are met.
Source: McAfee
The malware is capable of executing the following commands:
- DevInfo: Gathers device and hardware information, including Android ID, brand, CPU, model, OS version, language, developer options status, SIM details, and firmware.
- GeoInfo: Determines the device’s geographic location using its IP address, collecting ISP name, organization, services, and a fraud score to detect non-genuine users.
- EmuInfo: Lists adbProperties to ascertain if the client is a real device or an emulator, checking CPU, memory, sensors, USB configuration, and ADB status.
- RootInfo: Identifies if the device is rooted using various methods and provides the rooting status.
- Packages: Lists all system and third-party apps installed on the device using system commands.
- Accessibility: Reports the status of accessibility services permissions.
- GetURL: Requests the second-stage payload from the C2 server by providing the Android ID and receives the status and potentially an encrypted assembly DLL.
McAfee has also found links between Xamalicious and an ad-fraud app called ‘Cash Magnet,’ which automatically clicks ads and installs adware on the victim’s device to generate revenue for its operators.
Therefore, it’s possible that Xamalicious also performs ad fraud on infected devices, diminishing processor performance and network bandwidth.
Although Google Play isn’t immune to malware uploads, initiatives like the App Defense Alliance aim to detect and remove novel threats that appear on the app store, which isn’t the case on unofficial and poorly moderated platforms.
Android users should avoid downloading apps from third-party sources, limit themselves to essential apps, thoroughly read user reviews before installation, and conduct a comprehensive background check on the app’s developer/publisher to limit malware infections on their mobile devices.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.