How do ransomware groups pick their targets? It’s a rhetorical question: in the vast majority of cases they don’t. Ransomware-as-a-service (RaaS) platforms and ransomware affiliate ecosystems do not operate alone, but instead, they rely on a sophisticated cybercrime supply chain that enables access to corporate IT environments.
Ransomware groups and affiliates in many cases don’t “choose” targets, they buy them.
Ransomware attackers are opportunistic criminals that exploit easily accessible targets, often leveraging initial access points provided by other cybercriminals, rather than creating these access points themselves.
In recent years, the cybercrime ecosystem has grown substantially in size, sophistication, and complexity. Much like our modern economy, there are now many independent supply chains operating together with complex interdependencies.
This article is going to examine multiple parts of the cybercrime supply chain and provide context for how they work together to cause the explosion in cybercrime we’ve seen in the past two years.
The Rise of Infostealer Malware
In many cases, ransomware attacks begin as a result of “stealer logs,” artifacts of an infostealer malware infection. The past three years have seen the explosive growth of infostealers, a type of malware that steals all browser credentials, cookies, cryptocurrency wallet information, and other sensitive data from a single host, exports it to C2 infrastructure, then self terminates on the machine.
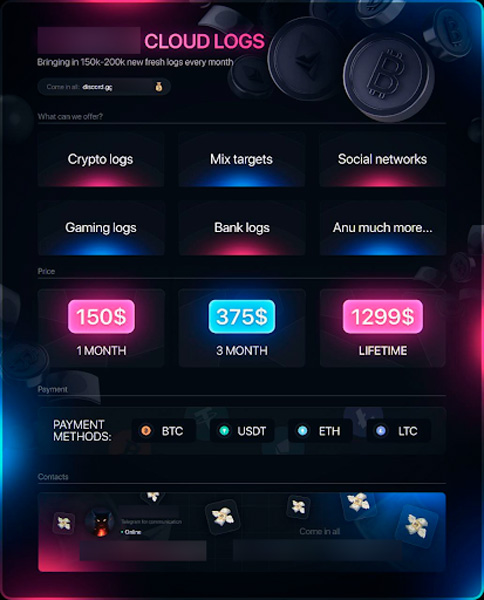
Specialized malware vendors create and sell variants of infostealer malware on Telegram channels, usually on a monthly or lifetime license model.
Other threat actors then purchase the licenses and distribute the malware through cracked software, malvertising, and phishing emails, before finally monetizing the resulting stealer logs.
A stealer log is a single compressed file that contains all of above mentioned information for a single user.
Illicit Telegram channels are the primary means that threat actors use to monetize their logs. Free channels serve as “samples” to prove that the actor has high-value and unique logs. These are advertisements for paid channels with a limited number of members that tend to have higher-value logs.
Flare has currently identified and ingested over 46 million stealer logs distributed across the dark web and Telegram, with each log containing up to hundreds of user credentials per infected device.
We currently see roughly 400,000 new infections per week, and estimate that approximately 5% contain corporate credentials.
Infostealers pose particularly acute risk due to the presence of session cookies within the stealer log. Active session cookies can be used for session replay attacks, where the actor is able to bypass multi-factor authentication.
Infostealers represent an extremely simple and straightforward mechanism for gaining initial access and establishing persistence to corporate IT infrastructure and systems.
While we suspect many ransomware groups and affiliates directly leverage access gained through infostealers, many others choose the “white glove” service that initial access brokers offer.
The Initial Access Broker Ecosystem
Initial access brokers are highly specialized threat actors who focus on carrying out the initial stages of an attack, gaining initial access to a corporate IT environment, and establishing persistence.
This access is then sold to other actors on three major dark web forums: Exploit, XSS, and RAMP, in an auction style format, or sold privately via direct messages in existing relationships.
Initial access brokers are a major source of supply for ransomware groups and affiliates. They remove a substantial barrier to entry, particularly for low-sophistication ransomware affiliates by establishing the privileged IT access and then auctioning it off.
Flare’s original research showed that initial access brokers compromised more than 500 companies in 2023, disproportionately target organizations located in NATO countries, and that compromised critical infrastructure sells for a premium.
Flare has seen direct evidence of initial access brokers purchasing “stealer logs in bulk.” These logs can then be sifted through to identify high-value credentials such as corporate emails, SSO portals, and development environments.
Exploiting Access: Ransomware Groups and Affiliates
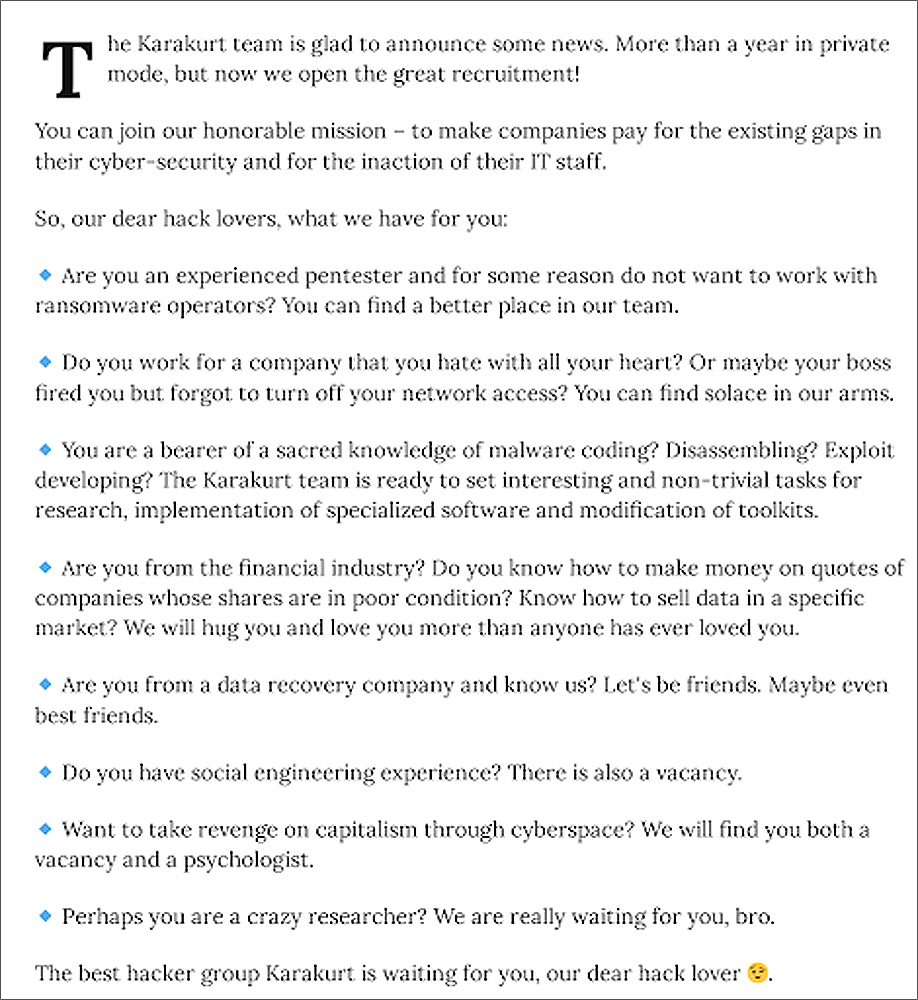
The ransomware economy continues to grow in complexity and sophistication. More than 50 ransomware groups are known to be in operation today, with many of them offloading work to affiliates.
Ransomware affiliates leverage the name recognition and software provided by the broader group in return for providing the group a cut of the profit.
Affiliates serve a critical role in the ecosystem. Competent affiliates allow a ransomware group to focus on developing increasingly sophisticated ransomware code and to perfect extortion techniques.
This role specialization builds efficiency across the criminal organization, resulting in more attacks, more payouts, and larger incentives.
Established ransomware groups often compete over top affiliates, as successful ransoms of major companies can bring in hundreds of thousands of dollars within days.
This competition was readily apparent during the recent episode on the Russian dark web forum XSS, in which LockBit accused the leader of CL0P of setting him up to be arrested by the FSB and even poisoned by polonium.
The cybercrime ecosystem is complex, and what we have detailed here is only a very brief and high-level overview of a significant and growing economy that spans TOR forums, Telegram, other social media, and even clear net sites.
Building a robust corporate continuous threat exposure management (CTEM) program, capable of disrupting every aspect of the cybercrime supply chain, is crucial in today’s environment.
Detect & Remediate Stealer Logs with Flare
The Flare Continuous Threat Exposure Management (TEM) solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors.
Our platform automatically scans the clear & dark web and illicit Telegram channels 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools.
Learn more by signing up for our free trial.
Sponsored and written by Flare.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.