French authorities arrested a Russian national in Paris for allegedly helping the Hive ransomware gang with laundering their victims’ ransom payments.
“New arrest in the Hive ransomware affair: after the international search in January to dismantle this network of hackers constituting a serious threat, the Judicial Police arrested in Paris an individual suspected of having laundered money from these cyber attacks,” the French National Police said (automated translation).
The suspect was apprehended after the French Anti-Cybercrime Office (OFAC) linked him to digital wallets that received millions of U.S. dollars from suspicious sources based on his activity on social networks.
Police agents also seized €570,000 worth of cryptocurrency assets when they detained the 40-year-old suspect and Cyprus resident on December 5, as first reported by LeMagIT.
“At the same time, the full cooperation with Europol, Eurojust and the Cypriot authorities made it possible to search his home in a Cypriot seaside resort, thus providing important elements of investigation,” said Nicolas Guidoux, a Deputy Director in the French Ministry of the Interior.
“On December 9, 2023, he was referred to the specialized prosecutor’s office of the Paris judicial court.”
This comes after Hive ransomware’s Tor websites were seized in January in an international law enforcement operation after the FBI infiltrated the gang’s servers in late July 2022.

This provided detailed information about Hive’s attacks before they occurred and helped warn their targets. The FBI also obtained and provided victims with over 1,300 decryption keys, preventing roughly $130 million in ransom payments from falling into the cybercriminals’ hands.
Besides decryption keys, the FBI and Dutch police also discovered Hive communication records, malware file hashes, and details on 250 Hive affiliates stored on Hive servers at a hosting provider in California and backup servers in the Netherlands.
The U.S. State Department is now offering up to $10 million for any information that could help link the Hive ransomware group (or other threat actors) with foreign governments.
In November, the FBI revealed that this ransomware operation had extorted around $100 million from over 1,500 companies since June 2021.
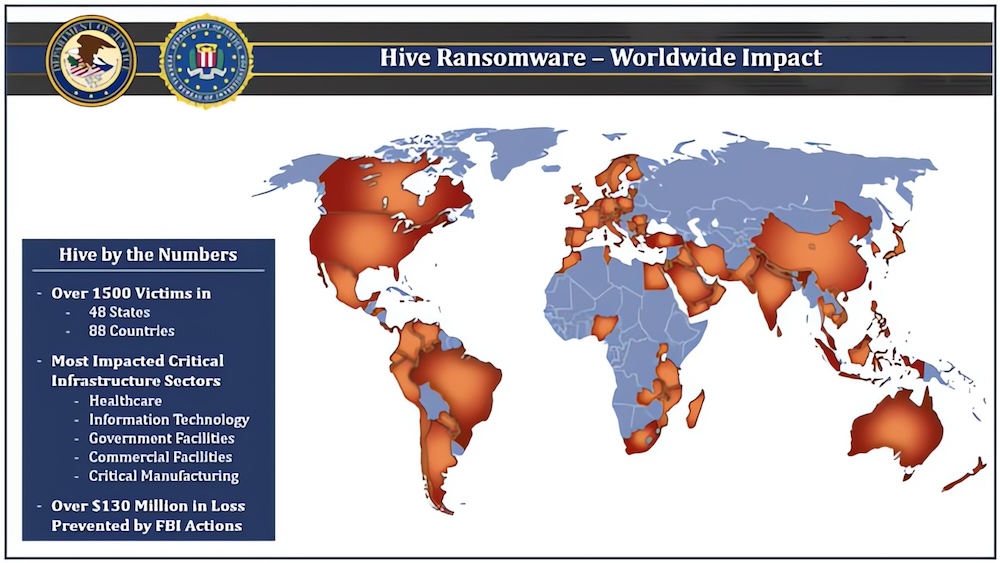
Hive operated as a ransomware-as-a-service (RaaS) provider for over two years since June 2019. It used phishing attacks, exploited vulnerabilities in internet-facing devices, and compromised stolen credentials to breach organizations.
Since law enforcement took down the gang’s infrastructure, a new ransomware-as-a-service (RaaS) operation named Hunters International has surfaced using code used by the Hive ransomware operation.
While analyzing a Hunters International ransomware sample, security researcher Will Thomas found code overlaps and similarities that matched over 60% of Hive ransomware’s code.
This led to the valid assumption that the old ransomware gang has resumed activity under a different brand.
Yet, the Hunters International collective refutes the researchers’ claims, dismissing them as “allegations,” saying they’re a new ransomware service that purchased the encryptor source code from Hive’s developers.
Moreover, the group claims that their primary focus isn’t encryption; instead, their operation’s primary goal is to steal data and use it to pressure victims into paying ransoms.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.