The LockBit ransomware operation is now recruiting affiliates and developers from the BlackCat/ALPHV and NoEscape after recent disruptions and exit scams.
Last week, the NoEscape and the BlackCat/ALPHV ransomware operation’s Tor websites suddenly became inaccessible without warning.
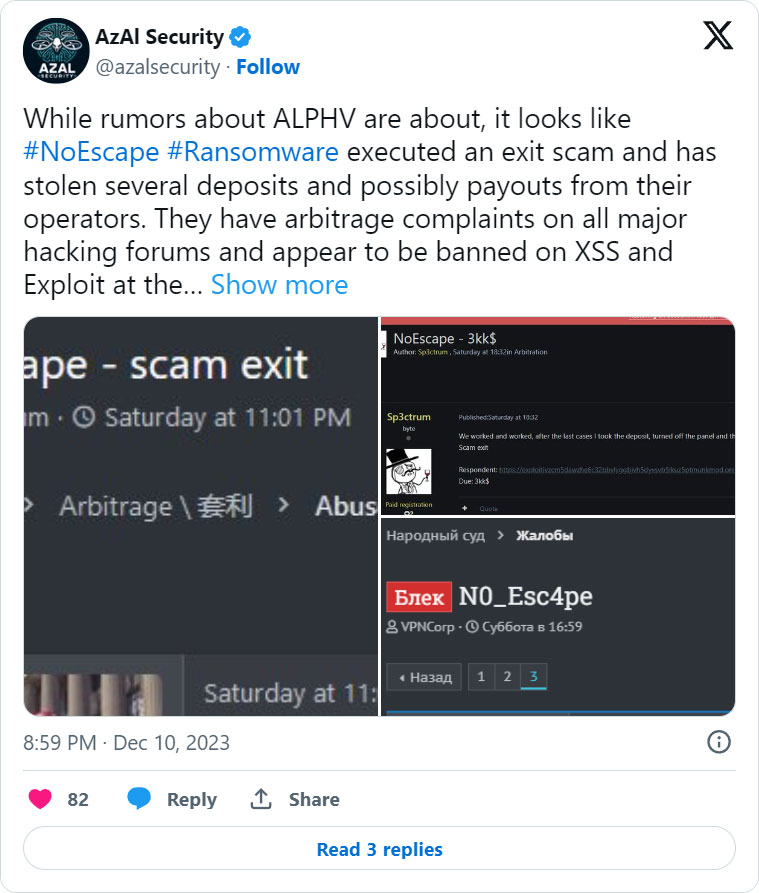
Affiliates associated with NoEscape claimed that the ransomware operators pulled an exit scam, stealing millions of dollars in ransom payments and shutting off the operation’s web panels and data leak sites.
NoEscape is believed to be a rebrand of the Avaddon ransomware operation, which shut down in June 201 and released their decryption keys to BleepingComputer. We hope that NoEscape will once again release the decryption keys for their victims now that they have shut down their operation.
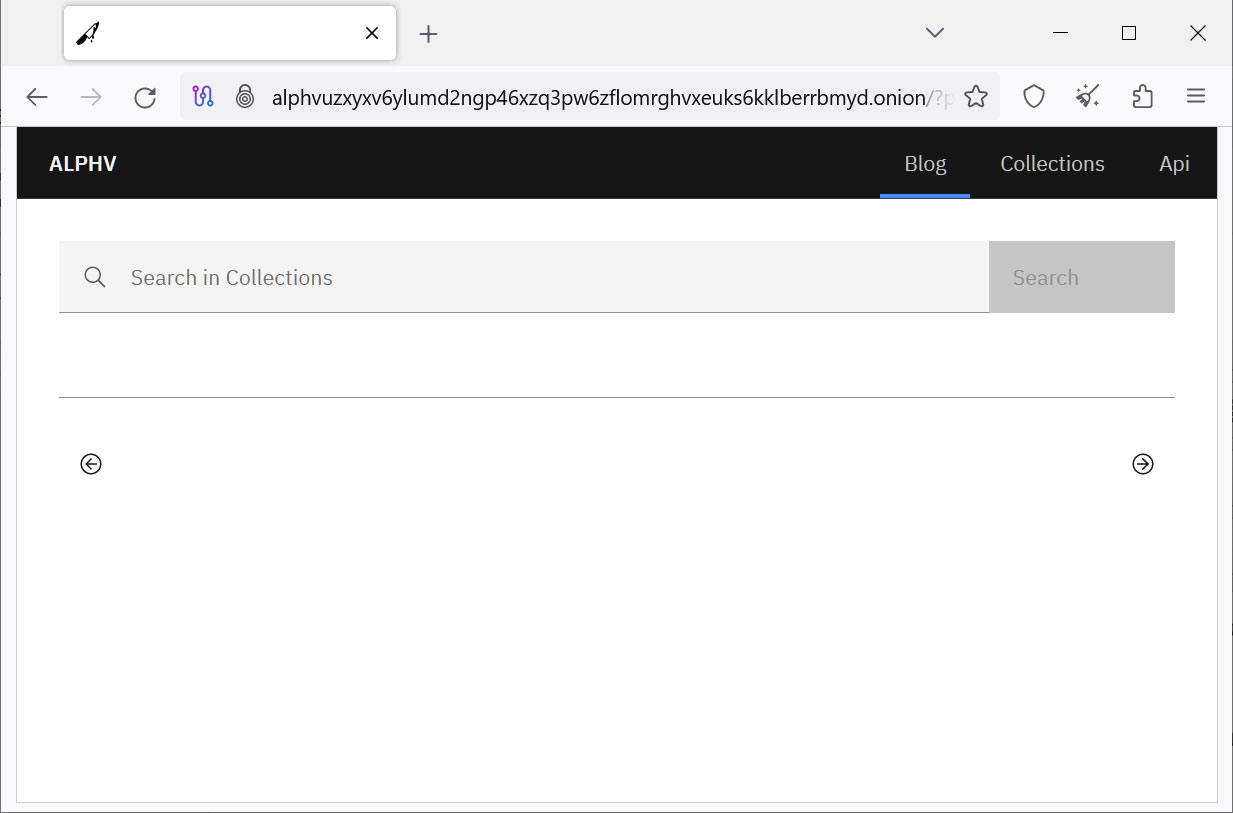
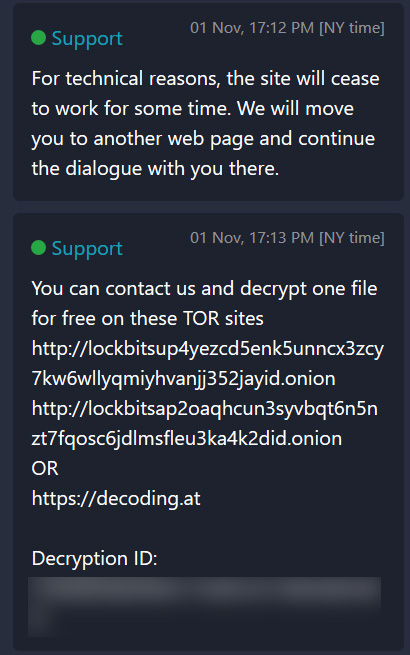
The BlackCat/ALPHV ransomware operation also suffered a 5-day disruption last week, with all their infrastructure going offline, including their data leak and negotiation sites.
On Monday, the ALPHV data leak site returned, but with all data removed. While some negotiation URLs are working, many are not, effectively halting negotiations for those victims.
Source: BleepingComputer
The ALPHV admin claimed that their outage was caused by hardware failure. However, BleepingComputer heard from multiple sources that a law enforcement operation was related to the outage.
The FBI declined to comment when we contacted them about the disruptions.
Are you an ALPHV or NoEscape affiliate or someone with information about the outages? If you want to share the information, you can contact us securely on Signal at +1 (646) 961-3731, via email at [email protected], or by using our tips form.
LockBit recruits affiliates from distressed gangs
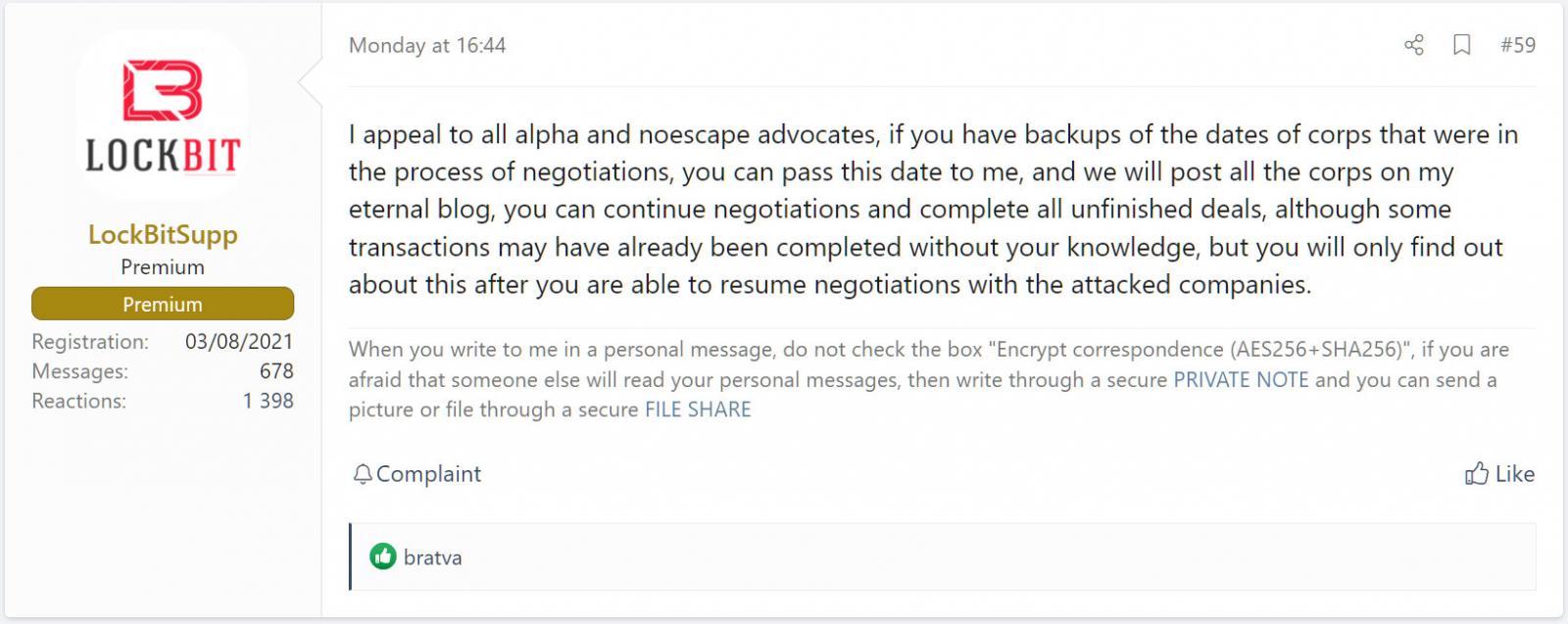
As first reported by LeMagIT, LockBitSupp, the LockBit operation’s manager, has begun to recruit affiliates from the BlackCat and NoEscape ransomware operations.
In posts to a Russian-speaking hacking forum, LockBitSupp told affiliates that if they have backups of the stolen data, they could use his data leak site and negotiation panel to continue to extort victims.
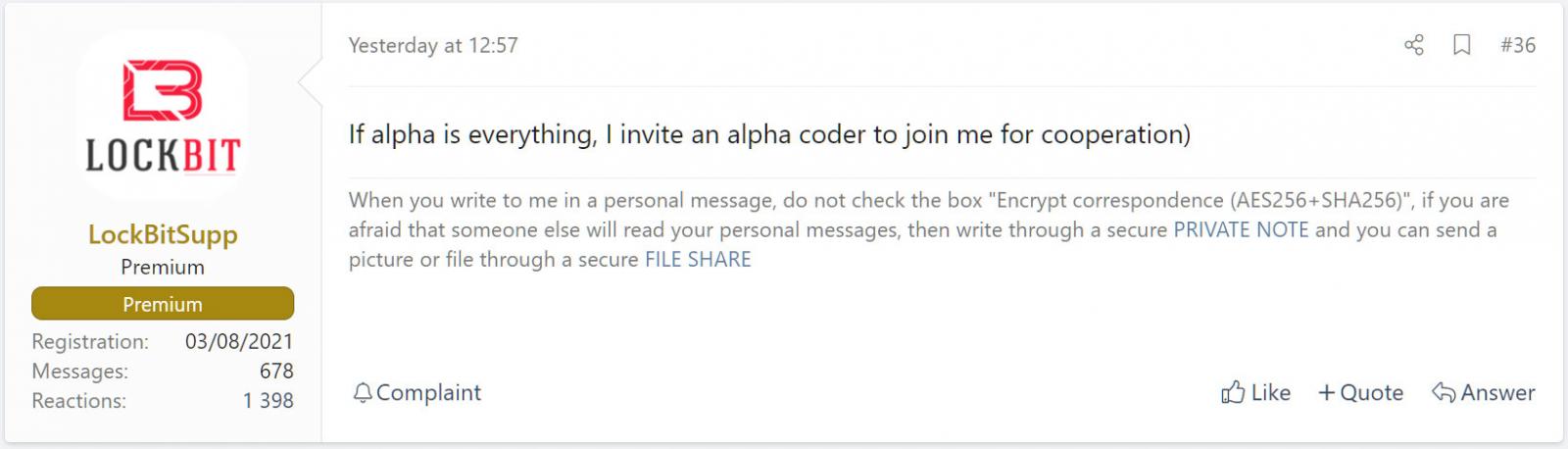
In addition to affiliates, LockBitSupp is trying to recruit the coder for the ALPHV encryptor.
While it is unclear if any of the BlackCat/NoEscape affiliates have moved over to LockBit, one BlackCat’s victim has already been spotted on LockBit’s data leak site.
“LockBit ransomware group has added German Energy Agency dena (http://dena.de) to their victim list, which was previously a victim of ALPHV ransomware group,” reads a tweet from FalconFeeds.
BlackCat/ALPHV is a rebrand of the DarkSide and BlackMatter ransomware operations. After BlackMatter’s shutdown in November 2021, its affiliates transitioned to LockBit.
Source: BleepingComputer
With LockBit being the largest ransomware operation at this time, LockBitSupp told BleepingComputer that he viewed the BlackCat outages as a “Christmas Gift.”
It is too soon to tell whether affiliates and penetration testers have lost trust in BlackCat or NoEscape and are moving to other operations. However, it would not be surprising if we soon see another rebrand.
This content is being syndicated from Source link for documentation purpose. If you are the owner of the content and like it removed, kindly contact me here and I will remove the content.